Expeditions with MCUP
Establishing Control Potential
Leveraging Competition for Domain Advantage in Modern Warfare
Bryan Leese, PhD
20 March 2026
https://doi.org/10.36304/ExpwMCUP.2026.04
PRINTER FRIENDLY PDF
EPUB
AUDIOBOOK
Abstract: This article explores the importance of using peacetime influence during competition to establish control potential before conflict in modern warfare. The Joint Warfighting Concept (JWC), a threat-informed framework designed to guide the U.S. Joint Force in preparing for future modern conflicts, is central to the discussion. The JWC also serves as a domain-control strategy to increase influence in key operational areas, creating an advantage for expanded maneuver and pulsed operations. However, the JWC lacks guidance on identifying the specific key battles to secure a strategic advantage. This article reviews J. C. Wylie’s domain control theories and Milan Vego’s prerequisites for domain control. It introduces a control potential (Cp) methodology to help military planners achieve an advantage through competition, thereby increasing the chances of gaining domain control in conflict. The Cp methodology can be a valuable tool in developing combatant commander campaign plans by making them more informed.
Keywords: Joint Warfighting Concept, JWC, domain warfare, J. C. Wylie, Milan Vego, control potential
Introduction
The four turbofan engines roared to life; the first of seven Northrop B-2 Spirit stealth bombers took off, heading for targets in Iran, more than 11,000 kilometers away. Operation Midnight Hammer (22 June 2025) integrated more than 100 U.S. aircraft, cyber and space effects, and sea-launched Tomahawk missiles to suppress Iran’s air defenses and create an opening. The bombers exploited that opening, attacking their targets, Iran’s nuclear weapons development sites, and returning home safely. The operation highlights a crucial truth about modern warfare: the U.S. Joint Force succeeded not only through a well-planned attack but also because it won the key battles for domain advantage before the fight. The forward-sensing nodes, robust space-based communications, improved weapons systems, and maritime partnerships gave U.S. commanders a critical advantage before the operation even began.[1]
This article argues that the Joint Warfighting Concept (JWC) is a threat‑informed concept describing how the Joint Force operates and fights as an integrated team across all domains. It is fundamentally a domain-control strategy—one that creates potential, broadly defined as the transformation of resources into influence, setting conditions for future domain control during conflict. The competition is a constant struggle for advantage, or what the JWC calls “key battles for advantage.”[2] Any control strategy must focus on gathering the prerequisites for gaining, maintaining, exploiting, or disputing domains to achieve military objectives in war. The key aspect of the JWC is that it aims to leverage competition to generate influence that enhances the potential for control before conflict. However, the JWC offers little guidance on determining where the key battles for advantage lie and how winning them creates control and an advantageous starting position that enables success. This article suggests that the concept of control potential provides the missing link and proposes a methodology to help commanders understand, measure, and intentionally develop campaign plans to gather prerequisites for control across critical warfighting domains.
To make this case, the article first clarifies the foundations of domain control theory by drawing on the work of U.S. Navy rear admiral J. C. Wylie, military historian Herbert Rosinski, U.S. Navy rear admiral Henry E. Eccles, and U.S. Naval War College professor Milan Vego on strategy and modern multidomain conditions, distinguishing between influence and control. Second, it translates these theoretical insights into a multidomain context, showing how control potential is gained or denied across land, maritime, air, cyber, and space environments, and why the competition phase—not conflict—is where decisive advantages are formed. Third, it offers a practical control potential (Cp) net assessment methodology that planners can apply to identify gaps, prioritize investments, and link the JWC to the cumulative and sequential mechanisms that generate strategic and operational advantage.
In short, just as Operation Midnight Hammer demonstrated, the Joint Force cannot wait for conflict to establish control. It must deliberately and systematically build Cp and win the key battles for advantage through competition across all domains, so that the first move in a crisis begins from a position of strength rather than parity.
Domain Control Theory Influence and Control
There are notable similarities between the JWC and the United States’ late Cold War-era AirLand Battle doctrine that led to victory over the Soviet-equipped Iraqi forces in Operation Desert Storm (1991).[3] Since then, the scale and speed of war have increased, and today’s commanders have less time to sense and make sense of the changing environment, to decide, and to act.[4] Additionally, technology has introduced a widespread threat of long-range kinetic and nonkinetic fires, antiaccess and area-denial conditions, and ongoing contention in the cyber and space domains by multiple state and nonstate actors.
To understand how to establish an advantage, it is important to examine domain control theory, which offers insights into how physical and cognitive elements interact and influence one another. By employing control through direct action or influence through subtle means, one can effectively manage the complexities of both competition and conflict. Such understanding links the JWC to international relations and strategic competition, two elements reflected in the combatant commander’s three- to five-year theater campaign plan. The plan’s design reinforces the importance of integrated use of the levers of national power to shape global outcomes. Still, at the core of the campaign is a military strategy that views the military lever and control as the fulcrum of national power.[5]
A small group of military theorists at the U.S. Naval War College examined the idea of creating or denying control as the essence of strategy. Historian Nicholas C. Prime described the collective efforts of Rosinski, Eccles, and Wylie in the 1950s as the “control theory school.” They explored historical naval strategy, concluding that “strategy itself is a matter of control.”[6] Within an operational environment, control is the physical or psychological pressure, or power, that elicits a desired response from a competitor or adversary when applied to elements of a domain system. Simply put, applying power or influence to a component of a domain system creates conditions conducive to achieving objectives.[7]
In Military Strategy: A General Theory of Power Control, Wylie describes the ultimate form of domain control as coming from a “man on the scene with the gun.”[8] This definition falls short in the cyber and space domains, where access, persistence, effects, and attribution manifest differently. Still, examining sea control theory provides an opportunity to demonstrate control as a form of strategic power. Vego, borrowing from naval theorists Alfred Thayer Mahan and Julian S. Corbett, summarizes sea control as “one’s ability to use a given part of the sea/ocean and associated air (a factor of space) for military and nonmilitary purposes and deny the same to the enemy in time of open hostilities.”[9] Holistically, in war, the aim is to reduce the enemy’s control while increasing one’s own. To gain domain control in war, one must set conditions, or a favorable starting point, for doing so. That position most often results from successful long-term strategic competition below the level of conflict.
The control theory school began its consideration from the perspective of physical force. Wylie offered two mechanisms for achieving control—cumulative and sequential—which must be coordinated.[10] The cumulative approach used small activities and investments to reduce an enemy’s power, increasing one’s control over time. No single event is decisive; rather, control emerges from the total impact over time. Because the cumulative approach involves denying or contesting the adversary’s control, it lends itself to the maritime, air, space, and cyber domains. The sequential mechanism uses a connected chain of actions, each building on the last. Wylie published his work during the Cold War (1967) and observed that sequential strategies predominate in land campaigns because of the nature of that domain. Wylie never intended to make a domain distinction between the cumulative and sequential approaches; they were general theories of control across domains, not a domain-specific taxonomy, but complementary mechanisms.
An example of cumulative and sequential approaches can be seen in Ukraine’s defense against Russia’s initial invasion in 2022, which illustrates the effective integration of these approaches. Ukrainian land forces executed a sequential defense of Kyiv, conducting a series of interconnected actions that delayed and disrupted Russian advances. Complementing this approach were cumulative effects in the air, maritime, cyber, and space domains. Persistent drone reconnaissance, attacks, and multidomain air defense strategies exploited opportunities to degrade Russian control and operational tempo through a series of dispersed actions rather than a single decisive encounter. Commercial space-based assets provided vital situational awareness, enhancing both cumulative actions and the targeting precision necessary for ground operations.[11]
Figure 1. Russian tank column being ambushed in Brovary, on the outskirts of Kyiv, by Ukrainian forces

Source: “Ukraine War: Column of Russian Tanks Ambushed by Ukrainian Forces,” BBC, 10 March 2022.
A Struggle for Control
Vego writes extensively on sea control, but his observations and theories apply to all domains. Like Wylie, Vego notes similar conditions and degrees, and that achieving the desired level depends on factors of time, space, and available force. Since the primary mechanism for gaining and maintaining control involves combat or the threat of combat, Vego describes it as a “struggle for control,” which has three phases: 1) gaining and maintaining; 2) exploiting the control to obtain an objective; and 3) disputing the enemy’s control. Vego’s examination suggests that the struggle for control is aided when one has certain “prerequisites.” A favorable position in the domain, such as a base of operations or control of a choke point, is important. That position can also be transdomain, in which an advantage in one domain may translate into securing or contesting control in another. One also needs a balanced force with numerical and or qualitative superiority, sound military doctrine, close cooperation among Services (Jointness) and allies, an offensive spirit, and information superiority.[12]
The early phase of the 2022 Russian invasion of eastern Ukraine also illustrates the advantage of having prerequisites. Russia leveraged its favorable position in Crimea and the Rostov Oblast and its large, well-equipped, multidomain forces to successfully secure Ukraine’s southern coastline, connecting Russia, Crimea, and the occupied eastern territories. When Russian forces sought to use the same maritime advantage to expand land control westward, Ukrainian forces, who also had a favorable position, allies and partners, and an offensive spirit but limited naval power, disputed Russia’s maritime dominance. The Ukranians exploited their advantages in the cyber and air domains, destroying naval combatants and supporting vessels and thwarting Russia’s push westward.[13] This example illustrates that gathering prerequisites for domain control is an intermediate objective of a cumulative, sequential campaign, but even with substantial control power, such as the Russian Navy’s Black Sea Fleet, domain control relies not solely on force but also on aligning clear operational goals with control of critical asymmetrical features inside multiple domains that enable persistent influence.[14]
Figure 2. Russian cruiser Moskva being towed after suffering damage in the Black Sea, 19 April 2022; the warship later foundered and sank

Source: “Moskva Warship Sinking—37 Sailors Dead, 100 Injured: Russian Media,” Defense Mirror, 19 April 2022.
Military power holds importance even in times of peace. The Wylie-led group focused on control from a war perspective rather than a peacetime competitive one. Vego argues that there is no sea control during peacetime; it exists only during wartime. He believes this because the sea is a “great commons,” similar to cyberspace, space, and parts of the air domains, making these areas part of economic competition during peace. Vego recognizes that influence within a domain arises through competition before armed conflict, and that such competition generates influence that may translate into an advantage when conflict arises. His concept of influence as essential for gaining control provides the context for control potential. If control is reserved for wartime, then control potential is the vital peacetime precursor. Creating potential involves coordinating cumulative influencing activities during competition. Through both competition and cooperation, military operations, activities, and investments can build relationships, strengthen alliances, create influence, and set conditions that may someday enable domain control in a future conflict.
Gathering Prerequisites under Fire
If the United States does not create control potential before a conflict, it must gather prerequisites while fighting, a situation that the U.S. military faced in the Pacific theater of World War II and one it likely prefers to avoid in the next fight. In a 2023 article, the then-chairman of the Joint Chiefs of Staff, U.S. Army general Mark A. Milley, described the tenets of pulsed operations and the expanded battlefield as critical to exploiting advantages over the United States’ adversaries.[15] There is a connection between pulsed operations and “raiding” as a cumulative approach to gathering or contesting control prerequisites. Wylie and the control group recognized the implications of raiding, but Vego makes the linkage more explicit. The point is that the modern pace of warfare may not allow time to execute a cumulative strategy to assemble the prerequisites for control while under fire.
Past multidomain conflicts illustrate JWC tenets. For example, privateers during the American Revolutionary War (1775–83) and the Anglo-French War (1778–83) employed expanded maneuvering, combined with pulsed raiding, as a cumulative approach.[16] Raiding remains a pragmatic way for a weaker force to dispute control by denying prerequisites. The Russo-Ukrainian War provides modern examples. Ukraine targeted Russian energy infrastructure with deep drone strikes, successfully attacking the large Ust-Luga fuel processing and shipping terminal, 870 kilometers inside Russia.[17] The Ukrainians created cyber-physical operations by synchronizing effects across multiple domains. The deployment of malware-equipped drones to prevent Russian attempts to reuse or reverse engineer the technology is a glimpse of creative forms of raiding across multiple domains.[18] Russia now must protect distant lands inside its home territory, diffusing its concentration of force against Ukrainian targets.
Figure 3. Long-range drone attacks during the Russo-Ukrainian War, as of March 2024
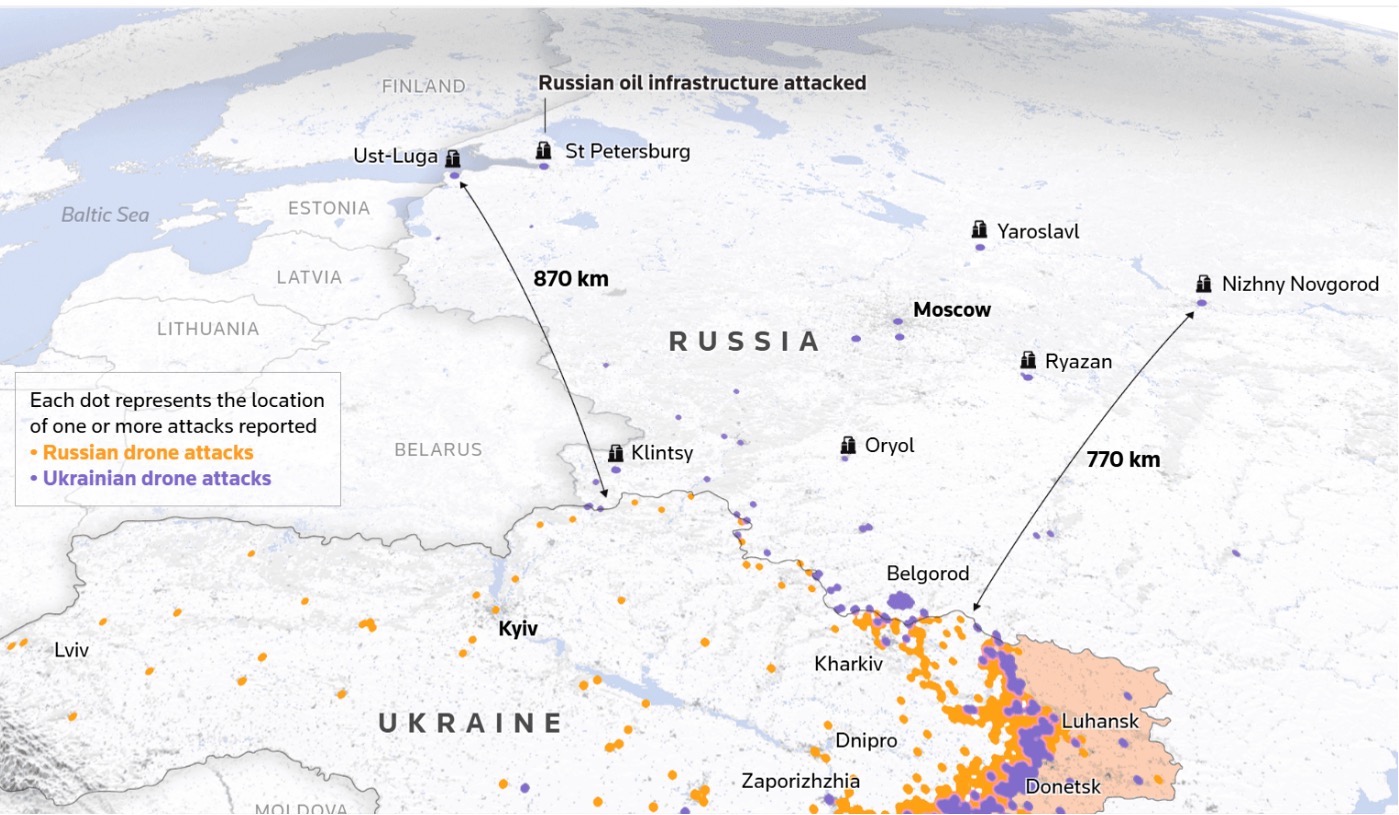
Source: Mariano Zafra et al., “How Drone Combat in Ukraine Is Changing Warfare,” Reuters, 26 March 2024.
Today’s JWC domain influence and control strategy emphasizes raiding across multiple domains; however, it must prioritize a whole-of-government effort to build control potential during competition, because the United States is already behind in this regard.[19] In a future conflict in the Pacific, the U.S. military is likely to begin from a strategic defensive posture across multiple domains. Technology has made future fights long-range, multidomain, and more deadly; they are likely to include attacks in cyberspace, space, and the air over the U.S. homeland. China has gained influence and developed sufficient capabilities, giving it a significant advantage.
Assessment Approach
Analyzing and assessing control potential is a complex but familiar task because the Cp methodology employs a net assessment approach that has long been a key multidisciplinary tool for the U.S. defense community to understand long-term strategic competition. Net assessment is comparative, diagnostic, and forward-looking; it views state interactions as inherently competitive rather than cooperative. The framework is intended to diagnose strategic asymmetries and identify opportunities for policymakers in strategy development.[20] For Cp, the net assessment process differs from the traditional method of directly comparing two competing systems. Cp provides a component-level comparison across multiple factor categories. The evaluation criteria for Cp include technology, influence operations, and Vego’s six prerequisites for control, categorized into the following factors: strategic position and bases; balanced force (capability and capacity); numerical versus qualitative force; doctrine and training; Jointness and offensive spirit; and information superiority.
To improve the utility of Cp, weights are assigned to the eight-factor framework. The weighted values yield a number that summarizes Blue’s advantage toward achieving control in a conflict scenario (e.g., the Luzon Strait, space-based assets such as Lagrange points, the Northern Philippines) for a specific time window. Analysts assign the weighted score based on specific time windows and scenario-specific conditions, such as the speed of the fight (e.g., fast or slow) or the character of the fight (e.g., gray-zone or direct), for each scenario. Gates, or a range of scores (e.g., 1–5), can also be set to stress that losing a prerequisite, such as intelligence, surveillance, and reconnaissance (ISR), removes other advantages, such as command and control, while a gain might increase them.
The analyst evaluates the category within the given scenario and judges each factor by asking, “Is Blue better, worse, or the same as Red, and by how much?” The methodology depends on assessing factors, so it is subjective and must begin with a relevant and realistic threat scenario. Developing scenarios requires deep insight into the strategic and operational environments, competitors’ capabilities, and one’s strengths and weaknesses as well as those of one’s partners and allies. Using an integrated team of intelligence professionals and operators to develop the scenarios is critical to their usefulness. Common threat scenarios used in the U.S. military’s integrated planning process and as part of the strategic planning frameworks might be the best option.[21] To improve the Cp methodology, increasingly specific threat scenarios are needed that focus on particular competitors (e.g., China, Russia, Iran), strategic positions or decisive points (e.g., choke points, networks, commercial industries), or future strategic goals and conditions that remain only partially understood.
Also important are the factor assessments performed by analysts. Creating rubrics to help analysts make assessments is essential. Rubrics reduce bias and enable multiple intelligence and operations research/system analysis groups to apply analytic tradecraft more consistently, producing analyses that are repeatable across organizations. Having several organizations perform assessments is part of a competitive analysis process that the U.S. intelligence community has relied on for decades.[22] Wargaming scenarios can bring intelligence organizations and operators together, also improving the analysis.
With the foundational elements of Cp methodology established, table 1 uses fictional data for an imaginary Red and Blue military, without a specified threat scenario, to further illustrate the methodology. The scores for each factor are on a 100-point scale. The weight is a percentage assigned to each factor that reflects its importance within the scenario. The relative difference and weighted differences of each factor are “within” the factor comparisons; positive numbers indicate an advantage for Blue, whereas negative numbers indicate an advantage for Red.
Using table 1, potential for control emerges in two perspectives: either the number of factors that Blue can influence (within factors) or the advantage that Blue has over Red in those factors (between Blue and Red analysis). From the “within” perspective, Blue’s weighted score across all factors is 68 percent, indicating a moderate potential for control in the evaluated scenario. Blue may feel that this is sufficient and seek to maintain its current strategy. Blue may, on the other hand, feel that it needs greater control potential and focus on strengthening its weaker areas, such as information superiority, identified during the “within factors” analysis. The Blue perspective, which focuses solely on its potential (68 percent), could lead to an inward-looking organizational myopia in which solutions are driven by internal preferences rather than by external competition.[23]
Table 1. Illustrating the Cp methodology
|
Factor
|
Weighted (w)
|
Red
|
Blue
|
Red (w)
|
Blue (w)
|
Relative Difference
|
Weighted (w) Difference
|
| |
Value
|
Value 1–100
|
Value 1–100
|
|
|
|
|
|
Strategic position and bases
|
18%
|
90
|
75
|
0.162
|
0.135
|
-15
|
-0.02
|
|
Balanced force (capability/capacity)
|
15%
|
70
|
65
|
0.105
|
0.097
|
-5
|
-0.01
|
|
Numerical and qualitative
|
12%
|
50
|
80
|
0.06
|
0.096
|
30
|
0.04
|
|
Doctrine/training
|
12%
|
70
|
75
|
0.084
|
0.09
|
5
|
0.01
|
|
Jointness and spirit
|
12%
|
80
|
55
|
0.096
|
0.066
|
-25
|
-0.03
|
|
Information superiority
|
13%
|
70
|
30
|
0.091
|
0.039
|
-40
|
-0.05
|
|
Technology
|
10%
|
50
|
90
|
0.05
|
0.09
|
40
|
0.04
|
|
Influence operations
|
8%
|
65
|
85
|
0.052
|
0.068
|
20
|
0.02
|
|
Total
|
1
|
545
|
555
|
0.700
|
0.682
|
10
|
-0.02
|
Note: The author proposed the idea of analysis to assess “potential” in a 2017 article, without suggesting any specific methodology to do so. See Cdr Bryan H. Leese, USN, “Living in TACSIT 1,” U.S. Naval Institute Proceedings 143, no. 2 (February 2017). The author would like to thank his brother, LtCol Jared Leese, USAF (ANG), and his wife, Elizabeth Leese, M.S.Ed., for their help in developing the table.
Source: courtesy of the author.
The “between” analysis shifts the perspective to a comparative one, based on Blue’s weighted advantage over Red. The weighted advantage perspective is more useful, and Cp is defined as the weighted difference between Blue and Red’s potential for control for that scenario. For example, the Cp value of -0.02 offers insight for the theater commander. Blue’s potential for control relative to that of Red is likely not enough—Red has a Cp advantage, but with such a small number (-0.02), there is probably more parity than advantage. With sufficient data and statistical analysis, it is possible to determine whether Red’s -0.02 advantage is statistically significant, helping to understand “how much of an advantage” one side has.
When all factors in table 1 are considered, the snapshot in time shows that the potential to control is essentially balanced—which is interesting. What is fascinating is what the “within” factor analysis can reveal to Blue. Red’s homefield advantage, reflected in its benefits in the factors of strategic position and bases, balanced force, Jointness and spirit, and information superiority, offset Blue’s advantage in size and quality, reflected by the factors of numerical and qualitative, doctrine and training, technology, and influence operations. Fleshing out table 1 with a narrative explaining the advantages and disadvantages of each score provides insight beyond the numbers, which is important for decision makers (table 2).
Table 2. Example of Cp analysis table including narrative
|
Factor
|
Blue
|
Red
|
Recommendation for Blue
|
|
Strategic position and bases
|
Broad forward posture across country X and Y, plus nine defensive counterair sites in Z, expanding access and dispersal near the significant defensive line of antiair.
|
Concentrated “homefield” advantage in geography backed by long-range weapons that create maritime access challenges and hold the Blue supply base at W at risk, reinforcing the near seas positional advantage.
|
Harden and disperse air and maritime nodes using expeditionary approaches, build deception and rapid repair capacity, and continue distributed operations to complicate Red targeting.
|
Source: courtesy of the author.
In the example, what is important to the combatant command campaign planners is determining what might shift the Red advantage to Blue. In other words, where are the key battles for advantage? Because the methodology is weighted, Blue must focus on strengthening its forward posture and resilience (strategic positions and bases), which are the most significant factors (with a weight of 0.18). An improved strategic position is also likely to enhance the influence operations score. Utilizing allies and partners to increase access to strategic locations also boosts combined operations, thereby strengthening Jointness and spirit and supporting information superiority, along with technology improvements. Blue must improve the connected factors of ISR persistence and the resilience of its “kill web” of networks, sensors, and counter-ISR and targeting (C-ISRT) programs. While Blue improves its factor scores, it must undertake operations, activities, and investments as cumulative mechanisms within competition that systematically weaken Red’s advantages across the factors, especially information superiority, a persistent key battleground for advantage. The core idea of the Cp approach is recognizing that the eight factors are always interconnected.
The Cp methodology has the potential to enhance the military’s role in strategic competition by making campaign plans more relevant, as it focuses on strengthening JWC tenets by building a control advantage across all domains. Once competition escalates into conflict, the Cp methodology can help commanders determine where to apply cumulative and sequential control actions to gather or protect prerequisites while degrading the adversary’s capabilities. Using the Red versus Blue scenario in table 1, Blue would understand the value of focused cumulative kinetic and cyber actions against Red’s bases and networks, as well as information operations against the Jointness and spirit and information superiority areas. With this understanding in mind, the theater commander could develop preconflict domain-control contingency plans, design relevant exercises, and ensure appropriate readiness. In future force design and development, the Cp methodology supports JWC-focused industrial base efforts.
How does a commander determine if the competition campaign is shifting the Cp in their favor? For a Cp methodology to be effective and support a competition-focused campaign plan, it must support the long-range planning group, the operations planning element, the communication synchronization working groups, and the commander’s assessment board. The assessment plan may be the most important component of the Cp methodology; its consistent use of measures of effectiveness (MOEs) is crucial for evaluating whether the Cp is moving in the right direction.[24] The MOEs must be carefully developed to support the Cp methodology’s constant analysis, threat-scenario refinement, analysis-rubric refinement, and the “within” and “between” factor analyses. Without the MOEs, influence efforts might cause more harm than good to the potential for control when conflict occurs.
Conclusion
This article argues that the JWC is best understood and most usefully applied as a domain-control strategy that aims to use competition to produce position advantage. The Cp methodology provides a missing analytical bridge between competition campaigning and wartime domain control. In short, if one wants to start strong rather than starting even, one can use Cp to deliberately build advantage by identifying and winning key battles, and then carrying those advantages forward as the opening conditions for conflict.
The article began by clarifying a control theory foundation, linking Wylie’s cumulative and sequential mechanisms and Vego’s prerequisites for control to today’s multidomain operational environment, where control is contested across land, maritime, air, cyber, and space domains. Next, insights were translated into practice by proposing a scenario-driven, weighted Cp framework that compares Blue and Red on both “within” factors (how each side fares on the prerequisites) and “between” the sides (the net, weighted advantage). Finally, the article proposed that embedding Cp as a critical component of competition campaigning requires pairing analytic rubrics with MOEs and the commander’s assessments, showing decision makers where to invest, what to protect, and how to sequence operations that convert potential into control at the moment of need.
Several implications emerge from using Cp in campaign design and assessment. By treating Cp as a commander’s metric and integrating it into long-range and operational planning, it can be linked to key battles to enhance theater strategy. However, there are some concerns with the Cp methodology. As the British statistician George E. P. Box stated, “All models are wrong, but some are useful.” Cp may be helpful, but its analysis is most effective when connected to common threat scenarios used in strategic planning frameworks and to published analysis rubrics that promote consistency and competitive analysis. Using weighted factors allows the analysis to adapt to the evolving nature of the fight, but they also introduce potential bias. Future work on the methodology should focus on formalizing weight sensitivity and conducting more thorough red team reviews. The factors in the Cp methodology may be too shallow; expanding them to include industry and civil infrastructure dependencies, for example, better expresses the competitive and influence relationships. Incorporating automation and information management tools into the methodology execution is also necessary.
Recent operations underscore that success is enabled by advantages created well in advance. Modern conflicts show that access and posture, ISR persistence, networks, partners, deception, and resilience, rather than a single exquisitely planned strike, have strategic impacts. The Midnight Hammer vignette illustrates this: the Joint Force’s multidomain strike was possible because the U.S. military gathered the right prerequisites in competition, integrated their potential beforehand, and established control when and where required. Cp provides a practical way to choose where to fight for that advantage, how to invest to get it, and when to convert it into control. If the Joint Force institutionalizes Cp in its campaigns now, the first hours of the next crisis will not be a race to catch up, but the final turn of a contest it has already begun to win.
Endnotes
[1] David Cenciotti, “The U.S. Airstrike on Iran’s Nuclear Facilities Was 15 Years in the Making,” Aviationist, 26 June 2025.
[2] Adm Christopher W. Grady, USN, “Sharpening Our Competitive Edge: Honing Our Warfighting Capabilities through the Joint Warfighting Concept” (keynote address, Air & Space Forces Association, National Harbor, MD, 13 December 2023), 4, hereafter Grady keynote address.
[3] Adm Christopher W. Grady, USN, “Sharpening Our Competitive Edge: Honing Our Warfighting Capabilities through the Joint Warfighting Concept,” Joint Force Quarterly 111 (4th Quarter 2023): 16–24; and Grady keynote address.
[4] Sense and sense-making is a riff on U.S. military theorist John R. Boyd’s OODA loop (observe, orient, decide, act) model. See Maj David S. Fadok, USAF, “John Boyd and John Warden: Air Power’s Quest for Strategic Paralysis” (thesis, School of Advanced Airpower Studies, Air University, Maxwell AFB, AL, 1995).
[5] Both John J. Mearsheimer and Eliot A. Cohen provide the perspective. See John J. Mearsheimer, The Tragedy of Great Power Politics (Updated Edition), 1st ed. (New York: W. W. Norton, 2014); and Eliot A. Cohen, The Big Stick: The Limits of Soft Power and the Necessity of Military Force (New York: Basic Books, 2016).
[6] Nicholas C. Prime, “The Making of the Control School of Strategy: Joseph C. Wylie, Henry Eccles, and Herbert Rosinski at the U.S. Naval War College, 1950–1974” (PhD dissertation, King’s College London, 2017), 28.
[7] Prime, “The Making of the Control School of Strategy.”
[8] J. C. Wylie, Military Strategy: A General Theory of Power Control (Annapolis, MD: Naval Institute Press, 2014), 72.
[9] Milan Vego, Maritime Strategy and Sea Control: Theory and Practice (London and New York: Routledge, 2017), 24.
[10] Rich Ganske, “Joint Action: A Personal Theory of Power,” Medium, 28 May 2014. This essay offers a perspective on Wylie’s ideas of control, emphasizing coordination of the two elements.
[11] Andrew S. Bowen, Russia’s War in Ukraine: Military and Intelligence Aspects (Washingtn, DC: Congressional Research Service, 2023). See also Bradley Martin, D. Sean Barnett, and Devin McCarthy, Russian Logistics and Sustainment Failures in the Ukraine Conflict: Status as of January 1, 2023 (Santa Monica, CA: Rand, 2023), https://doi.org/10.7249/RRA2033-1; and “Communications and Cyber Security Troops,” Ministry of Defence of Ukraine, accessed 7 February 2026.
[12] Vego presents six prerequisites: a favorable domain strategic position that includes favorable bases of operations (position and number); a balanced force (capabilities and capacity); numerical/qualitative military superiority; sound military theory and doctrine/training; the closest cooperation among Services (Jointness) and an offensive spirit; and information superiority. Vego, Maritime Strategy and Sea Control, 54–68.
[13] Bowen, “Russia’s War in Ukraine.”
[14] Wylie, Military Strategy.
[15] Milley describes pulsed operations and expanded maneuver as critical elements of the JWC. Gen Mark A. Milley, USA, “Strategic Inflection Point: The Most Historically Significant and Fundamental Change in the Character of War Is Happening Now—While the Future Is Clouded in Mist and Uncertainty,” Joint Force Quarterly 110 (3d Quarter 2023): 10–12.
[16] Benjamin Armstrong, Small Boats and Daring Men: Maritime Raiding, Irregular Warfare, and the Early American Navy (Norman: University of Oklahoma Press, 2019). Armstrong’s concept of guerre de razzia (raiding war) is discussed in Zachary Griffiths, “Battlefield Lessons from the Swashbuckling Irregular Warfare of the Early American Navy,” Modern War Institute at West Point, 6 September 2019.
[17] Mariano Zafra et al., “How Drone Combat in Ukraine Is Changing Warfare,” Reuters, 26 March 2024.
[18] Miriam McNabb, “Ukraine’s Trojan Horse Drones: A New Frontier in Cyber Warfare,” DroneLife, 10 April 2025.
[19] See 2025 Report to Congress of the U.S.-China Economic and Security Review Commission (Washingtn, DC: Government Publishing Office, 2025).
[20] Thomas M. Skypek, “Evaluating Military Balances through the Lens of Net Assessment: History and Application,” Journal of Military and Strategic Studies 12, no. 2 (Winter 2010): 3.
[21] Joint Planning, Joint Publication 5-0 (Washington, DC: Joint Chiefs of Staff, 2025), iv.
[22] Mark M. Lowenthal, U.S. Intelligence: Evolution and Anatomy, 2d ed. (Westport, CT: Praeger; Washington, DC: Center for Strategic and International Studies, 1992), 116.
[23] Colin Grant, “Theodore Levitt’s Marketing Myopia,” Journal of Business Ethics 18, no. 4 (February 1999): 397–406, https://doi.org/10.1023/A:1005817506423. Levitt examined “market” and “competitor” myopia within business; his ideas apply to many organizational situations. Examples of organizational myopia are in the historic parochialism within the U.S. military Services. More recently, the slow realization described as “strategic atrophy” and eventual acceptance of China’s rise and the return of great power competition is another. See James N. Mattis, Summary of the 2018 National Defense Strategy of the United States of America: Strengthening the American Military’s Competitive Edge (Washington, DC: Department of Defense, 2018).